質問 1:Timing is an element of port-scanning that can catch one unaware. If scans are taking too long to complete or obvious ports are missing from the scan, various time parameters may need to be adjusted. Which one of the following scanned timing options in NMAP's scan is useful across slow WAN links or to hide the scan?
A. Sneaky
B. Paranoid
C. Polite
D. Normal
正解:C
質問 2:Which among the following information is not furnished by the Rules of Engagement (ROE) document?
A. Details on how organizational data is treated throughout and after the test
B. Techniques for data exclusion from systems upon termination of the test
C. Details on how data should be transmitted during and after the test
D. Techniques for data collection from systems upon termination of the test
正解:D
質問 3:Which Wireshark filter displays all the packets where the IP address of the source host is 10.0.0.7?
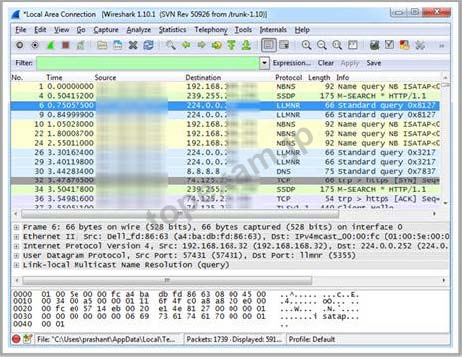 A.
A. ip.port==10.0.0.7
B. ip.dstport==10.0.0.7
C. ip.dst==10.0.0.7
D. ip.src==10.0.0.7
正解:D
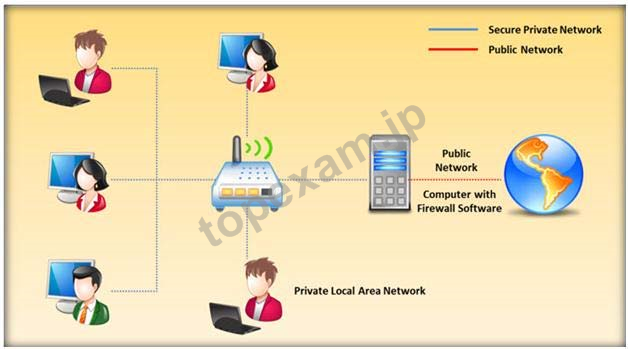
質問 4:Packet filtering firewalls are usually a part of a router. In a packet filtering firewall, each packet is compared to a set of criteria before it is forwarded.
Depending on the packet and the criteria, the firewall can: i)Drop the packet ii)Forward it or send a message to the originator
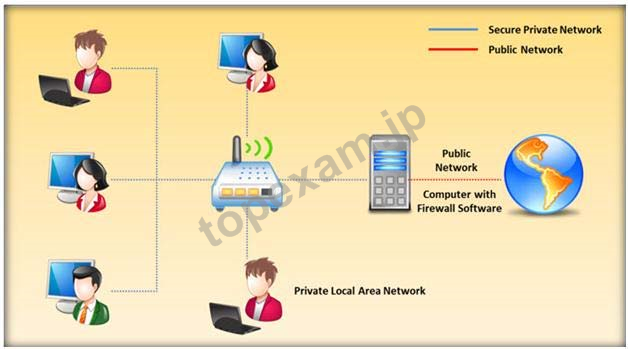
At which level of the OSI model do the packet filtering firewalls work?
A. Network layer
B. Application layer
C. Physical layer
D. Transport layer
正解:A
解説: (Topexam メンバーにのみ表示されます)
質問 5:The objective of social engineering pen testing is to test the strength of human factors in a security chain within the organization. It is often used to raise the level of security awareness among employees.

The tester should demonstrate extreme care and professionalism during a social engineering pen test as it might involve legal issues such as violation of privacy and may result in an embarrassing situation for the organization.
Which of the following methods of attempting social engineering is associated with bribing, handing out gifts, and becoming involved in a personal relationship to befriend someone inside the company?
A. Accomplice social engineering technique
B. Dumpster diving
C. Identity theft
D. Phishing social engineering technique
正解:A
質問 6:Which of the following is not a characteristic of a firewall?
A. Routes packets between the networks
B. Manages public access to private networked resources
C. Examines all traffic routed between thetwo networks to see if it meets certain criteria
D. Filters only inbound traffic but not outbound traffic
正解:D
質問 7:Assessing a network from a hacker's point of view to discover the exploits and vulnerabilities that are accessible to the outside world is which sort of vulnerability assessment?
A. Network Assessments
B. Application Assessments
C. External Assessment
D. Wireless Network Assessments
正解:C
解説: (Topexam メンバーにのみ表示されます)
質問 8:James is testing the ability of his routers to withstand DoS attacks. James sends ICMP ECHO requests to the broadcast address of his network. What type of DoS attack is James testing against his network?
A. Fraggle
B. Trinoo
C. SYN flood
D. Smurf
正解:D
質問 9:Which one of the following architectures has the drawback of internally considering the hosted services individually?
A. Strong Screened-Subnet Architecture
B. "Inside Versus Outside" Architecture
C. "Three-Homed Firewall" DMZ Architecture
D. Weak Screened Subnet Architecture
正解:C
一年間の無料更新サービスを提供します
君が弊社のEC-COUNCIL 412-79v8をご購入になってから、我々の承諾する一年間の更新サービスが無料で得られています。弊社の専門家たちは毎日更新状態を検査していますから、この一年間、更新されたら、弊社は更新されたEC-COUNCIL 412-79v8をお客様のメールアドレスにお送りいたします。だから、お客様はいつもタイムリーに更新の通知を受けることができます。我々は購入した一年間でお客様がずっと最新版のEC-COUNCIL 412-79v8を持っていることを保証します。
弊社は無料EC-COUNCIL 412-79v8サンプルを提供します
お客様は問題集を購入する時、問題集の質量を心配するかもしれませんが、我々はこのことを解決するために、お客様に無料412-79v8サンプルを提供いたします。そうすると、お客様は購入する前にサンプルをダウンロードしてやってみることができます。君はこの412-79v8問題集は自分に適するかどうか判断して購入を決めることができます。
412-79v8試験ツール:あなたの訓練に便利をもたらすために、あなたは自分のペースによって複数のパソコンで設置できます。
弊社は失敗したら全額で返金することを承諾します
我々は弊社の412-79v8問題集に自信を持っていますから、試験に失敗したら返金する承諾をします。我々のEC-COUNCIL 412-79v8を利用して君は試験に合格できると信じています。もし試験に失敗したら、我々は君の支払ったお金を君に全額で返して、君の試験の失敗する経済損失を減少します。
弊社のEC-COUNCIL 412-79v8を利用すれば試験に合格できます
弊社のEC-COUNCIL 412-79v8は専門家たちが長年の経験を通して最新のシラバスに従って研究し出した勉強資料です。弊社は412-79v8問題集の質問と答えが間違いないのを保証いたします。

この問題集は過去のデータから分析して作成されて、カバー率が高くて、受験者としてのあなたを助けて時間とお金を節約して試験に合格する通過率を高めます。我々の問題集は的中率が高くて、100%の合格率を保証します。我々の高質量のEC-COUNCIL 412-79v8を利用すれば、君は一回で試験に合格できます。
TopExamは君に412-79v8の問題集を提供して、あなたの試験への復習にヘルプを提供して、君に難しい専門知識を楽に勉強させます。TopExamは君の試験への合格を期待しています。
安全的な支払方式を利用しています
Credit Cardは今まで全世界の一番安全の支払方式です。少数の手続きの費用かかる必要がありますとはいえ、保障があります。お客様の利益を保障するために、弊社の412-79v8問題集は全部Credit Cardで支払われることができます。
領収書について:社名入りの領収書が必要な場合、メールで社名に記入していただき送信してください。弊社はPDF版の領収書を提供いたします。
EC-COUNCIL EC-Council Certified Security Analyst (ECSA) 認定 412-79v8 試験問題:
1. A pen tester has extracted a database name by using a blind SQL injection. Now he begins to test the table inside the database using the below query and finds the table:
http://juggyboy.com/page.aspx?id=1; IF (LEN(SELECT TOP 1 NAME from sysobjects where xtype='U')=3) WAITFOR DELAY '00:00:10'-
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((SELECT TOP 1 NAME from sysobjects where xtype=char(85)),1,1)))=101) WAITFOR DELAY '00:00:10'-
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((SELECT TOP 1 NAME from sysobjects where xtype=char(85)),2,1)))=109) WAITFOR DELAY '00:00:10'-
http://juggyboy.com/page.aspx?id=1; IF (ASCII(lower(substring((SELECT TOP 1 NAME from sysobjects where xtype=char(85)),3,1)))=112) WAITFOR DELAY '00:00:10'-
What is the table name?
A) QRT
B) CTS
C) EMP
D) ABC
2. Which one of the following components of standard Solaris Syslog is a UNIX command that is used to add single-line entries to the system log?
A) "Syslogd.conf"
B) "Syslogd"
C) "/etc/syslog.conf"
D) "Logger"
3. Which of the following scan option is able to identify the SSL services?
A) -sU
B) -sS
C) -sT
D) -sV
4. James is testing the ability of his routers to withstand DoS attacks. James sends ICMP ECHO requests to the broadcast address of his network. What type of DoS attack is James testing against his network?
A) Fraggle
B) Trinoo
C) SYN flood
D) Smurf
5. To locate the firewall, SYN packet is crafted using Hping or any other packet crafter and sent to the firewall. If ICMP unreachable type 13 message (which is an admin prohibited packet) with a source IP address of the access control device is received, then it means which of the following type of firewall is in place?
A) Packet filter
B) Stateful multilayer inspection firewall
C) Circuit level gateway
D) Application level gateway
質問と回答:
質問 # 1
正解: C | 質問 # 2
正解: D | 質問 # 3
正解: D | 質問 # 4
正解: D | 質問 # 5
正解: A |



 PDF版 Demo
PDF版 Demo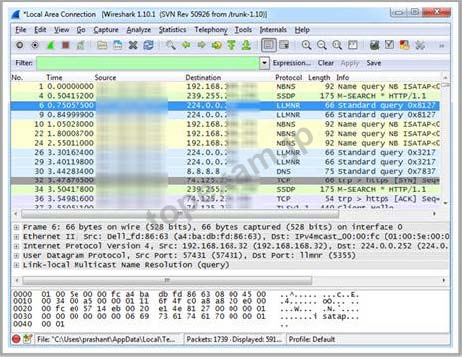







 品質保証TopExamは我々の専門家たちの努力によって、過去の試験のデータが分析されて、数年以来の研究を通して開発されて、多年の研究への整理で、的中率が高くて99%の通過率を保証することができます。
品質保証TopExamは我々の専門家たちの努力によって、過去の試験のデータが分析されて、数年以来の研究を通して開発されて、多年の研究への整理で、的中率が高くて99%の通過率を保証することができます。 一年間の無料アップデートTopExamは弊社の商品をご購入になったお客様に一年間の無料更新サービスを提供することができ、行き届いたアフターサービスを提供します。弊社は毎日更新の情況を検査していて、もし商品が更新されたら、お客様に最新版をお送りいたします。お客様はその一年でずっと最新版を持っているのを保証します。
一年間の無料アップデートTopExamは弊社の商品をご購入になったお客様に一年間の無料更新サービスを提供することができ、行き届いたアフターサービスを提供します。弊社は毎日更新の情況を検査していて、もし商品が更新されたら、お客様に最新版をお送りいたします。お客様はその一年でずっと最新版を持っているのを保証します。 全額返金弊社の商品に自信を持っているから、失敗したら全額で返金することを保証します。弊社の商品でお客様は試験に合格できると信じていますとはいえ、不幸で試験に失敗する場合には、弊社はお客様の支払ったお金を全額で返金するのを承諾します。(
全額返金弊社の商品に自信を持っているから、失敗したら全額で返金することを保証します。弊社の商品でお客様は試験に合格できると信じていますとはいえ、不幸で試験に失敗する場合には、弊社はお客様の支払ったお金を全額で返金するのを承諾します。( ご購入の前の試用TopExamは無料なサンプルを提供します。弊社の商品に疑問を持っているなら、無料サンプルを体験することができます。このサンプルの利用を通して、お客様は弊社の商品に自信を持って、安心で試験を準備することができます。
ご購入の前の試用TopExamは無料なサンプルを提供します。弊社の商品に疑問を持っているなら、無料サンプルを体験することができます。このサンプルの利用を通して、お客様は弊社の商品に自信を持って、安心で試験を準備することができます。
