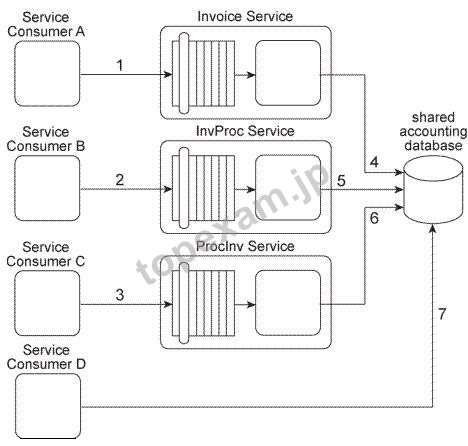
質問 1:Our service inventory contains the following three services that provide invoice-related data
access capabilities: Invoice, InvProc, and Proclnv. These services were created at different
times by different project teams and were not required to comply to any design standards.
Therefore each of these services has a different data model for representing invoice data.
Currently each of these three services has one service consumer: Service Consumer A
accesses the Invoice service(1). Service Consumer B (2) accesses the InvProc service,
and Service Consumer C (3) accesses the Proclnv service. Each service consumer
invokes a data access capability of an invoice-related service, requiring that service to
interact with the shared accounting database that is used by all invoice-related services (4,
5, 6).
Additionally, Service Consumer D was designed to access invoice data from the shared
accounting database directly (7). (Within the context of this architecture. Service Consumer
D is labeled as a service consumer because it is accessing a resource that is related to the
illustrated service architectures.)
A project team recently proclaimed that it has successfully applied the Contract
Centralization pattern to the service inventory in which the Invoice service, InvProc service,
and ProcInv service reside. Upon reviewing the previously described architecture you have
doubts that this is true. After voicing your doubts to a manager, you are asked to provide
specific evidence as to why the Contract Centralization is not currently fully applied. Which
of the following statements provides this evidence?
A. The Contract Centralization pattern is not fully applied because none of the invoice-
related services are carrying out data access logic via a centralized and standardized
invoice service. This is primarily because the Standardized Service Contract principle was
not consistently applied during the delivery processes of the individual services.
B. The Contract Centralization pattern is not fully applied to the Invoice, InvProc, and
ProcInv services because they are being accessed by different service consumers and
because they have redundant logic that introduces denormalization into the service
inventory.
C. The Contract Centralization pattern is not fully applied because Service Consumer D is
accessing the shared accounting database directly.
D. None of the above.
正解:C
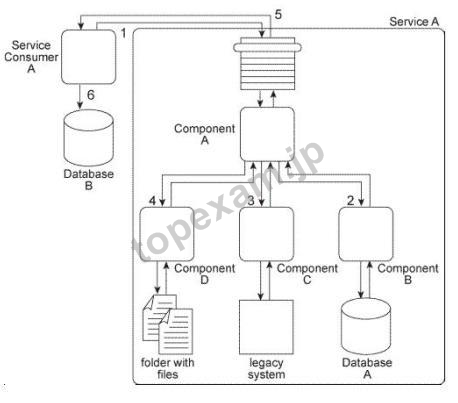
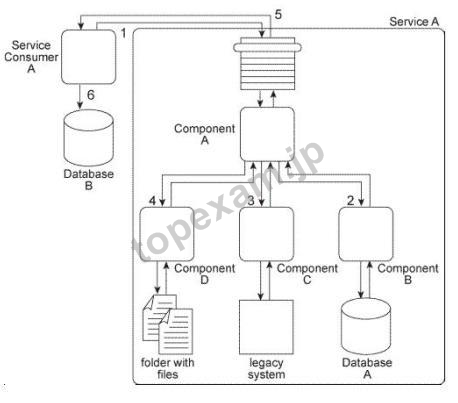
質問 2:When Service A receives a message from Service Consumer A(1),the message is
processed by Component A.
This component first invokes Component B (2), which uses
values from the message to query Database A in order to retrieve additional data.
Component B then returns the additional data to Component A.
Component A then invokes Component C (3), which interacts with the API of a legacy
system to retrieve a new data value. Component C then returns the data value back to
Component A.
Next, Component A sends some of the data it has accumulated to Component D (4), which
writes the data to a te>X file that is placed in a specific folder. Component D then waits
until this file is imported into a different system via a regularly scheduled batch import.
Upon completion of the import, Component D returns a success or failure code back to
Component A.
Component A finally sends a response to Service Consumer A (5) containing all of the data
collected so far and Service Consumer A writes all of the data to Database B (6).
Components A, B, C.
and D belong to the Service A service architecture. Database A, the
legacy system, and the file folders are shared resources within the IT enterprise.
Service A is an entity service with a service architecture that has grown over the past few
years. As a result of a service inventory-wide redesign project, you are asked to revisit the
Service A service architecture in order to separate the logic provided by Components B, C,
and D into three different utility services without disrupting the behavior of Service A as it
relates to Service Consumer A . What steps can be taken to fulfill these requirements?
A. The Legacy Wrapper pattern can be applied so that Component B is separated into a
separate wrapper utility service that wraps the shared database. The Asynchronous
Queuing pattern can be applied so that a messaging queue is positioned between
Component A and Component C, thereby enabling communication during times when the
legacy system may be unavailable or heavily accessed by other parts of the IT enterprise.
The Service Facade pattern can be applied so that a Facade component is added between
Component A and Component D so that any change in behavior can be compensated. The
Service Autonomy principle can be further applied to Service A to help make up for any
performance loss that may result from splitting the component into a separate wrapper
utility service.
B. The Legacy Wrapper pattern can be applied so that Component B is separated into a
separate utility service that wraps the shared database. The Legacy Wrapper pattern can
be applied again so that Component C is separated into a separate utility service that acts
as a wrapper for the legacy system API. Component D is separated into a separate service
and the Event-Driven Messaging pattern is applied to establish a publisher-subscriber
relationship between this new service and Component A.
The interaction between Service Consumer A and Component A is then redesigned so that Component A first interacts with
Component B and the new wrapper service. Service A then issues a final message back to
Service Consumer A.
The Service Composability principle can be further applied to Service
A and the three new wrapper utility services so that all four services are optimized for
participation in the new service composition. This will help make up for any performance
loss that may result from splitting the three components into separate services.
C. None of the above.
D. The Legacy Wrapper pattern can be applied so that Component B is separated into a
separate utility service that wraps the shared database. The Legacy Wrapper pattern can
be applied again so that Component C is separated into a separate utility service that acts
as a wrapper for the legacy system API. The Legacy Wrapper pattern can be applied once
more to Component D so that it is separated into another utility service that provides
standardized access to the file folder. The Service Facade pattern can be applied so that
three Facade components are added: one between Component A and each of the new
wrapper utility services. This way, the Facade components can compensate for any change
in behavior that may occur as a result of the separation. The Service Composability
principle can be further applied to Service A and the three new wrapper utility services so
that all four services are optimized for participation in the new service composition. This will
help make up for any performance loss that may result from splitting the three components
into separate services.
正解:D
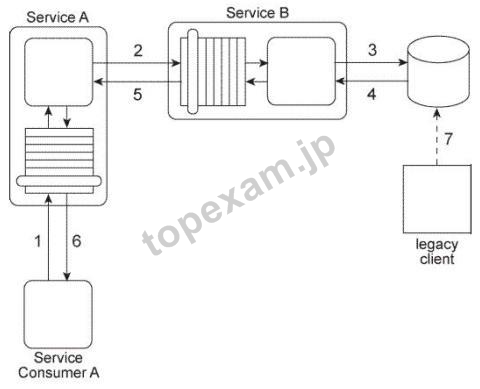
質問 3:Service A is an entity service that provides a Get capability that returns a data value that is
frequently changed.
Service Consumer A invokes Service A in order to request this data value (1). For Service
A to carry out this request, it must invoke Service B (2), a utility service that interacts (3.4)
with the database in which the data value is stored. Regardless of whether the data value
changed, Service B returns the latest value to Service A (5), and Service A returns the
latest value to Service Consumer A (6).
The data value is changed when the legacy client program updates the database (7) When
this change happens is not predictable. Note also that Service A and Service B are not
always available at the same time.
Any time the data value changes. Service Consumer A needs to receive it as soon as
possible. Therefore, Service Consumer A initiates the message exchange shown in the
Figure several times a day. When it receives the same data value as before, the response
from Service A is ignored. When Service A provides an updated data value, Service
Consumer A can process it to carry out its task.
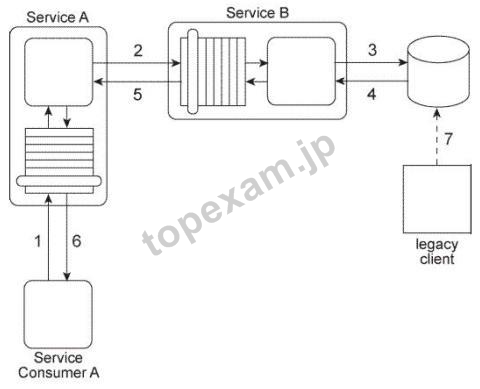
The current service composition architecture is using up too many resources due to the
repeated invocation of Service A by Service Consumer A and the resulting message
exchanges that occur with each invocation. What steps can be taken to solve this problem?
A. The Event-Driven Messaging pattern can be applied by establishing a subscriber-
publisher relationship between Service Consumer A and Service A . This way, every time
the data value is updated, an event is triggered and Service A, acting as the publisher, can
notify Service Consumer A, which acts as the subscriber. The Asynchronous Queuing
pattern can be applied between Service Consumer A and Service A so that the event
notification message sent out by Service A will be received by Service Consumer A, even
when Service Consumer A is unavailable.
B. The Asynchronous Queuing pattern can be applied so that messaging queues are
established between Service A and Service B and between Service Consumer A and
Service A . This way, messages are never lost due to the unavailability of Service A or
Service B.
C. The Event-Driven Messaging pattern can be applied by establishing a subscriber-
publisher relationship between Service A and Service B . This way, every time the data
value is updated, an event is triggered and Service B, acting as the publisher, can notify
Service A, which acts as the subscriber. The Asynchronous Queuing pattern can be
applied between Service A and Service B so that the event notification message sent out
by Service B will be received by Service A, even when Service A is unavailable.
D. None of the above.
正解:D
質問 4:Our service inventory contains the following three services that provide invoice-related data
access capabilities: Invoice, InvProc, and Proclnv. These services were created at different
times by different project teams and were not required to comply to any design standards.
Therefore each of these services has a different data model for representing invoice data.
Currently each of these three services has one service consumer: Service Consumer A
accesses the Invoice service(1). Service Consumer B (2) accesses the InvProc service,
and Service Consumer C (3) accesses the Proclnv service. Each service consumer
invokes a data access capability of an invoice-related service, requiring that service to
interact with the shared accounting database that is used by all invoice-related services (4,
5, 6).
Additionally, Service Consumer D was designed to access invoice data from the shared
accounting database directly (7), (Within the context of this architecture. Service Consumer
D is labeled as a service consumer because it is accessing a resource that is related to the
illustrated service architectures.)
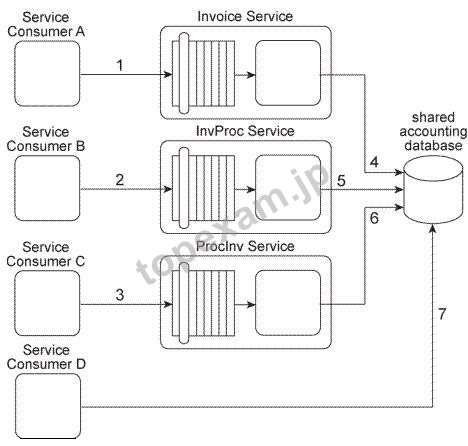
Assuming that the Invoice service, InvProc service, and ProcInv service are part of the
same service inventory, what steps would be required to fully apply the Official Endpoint
pattern?
A. One of the invoice-related services needs to be chosen as the official service providing
invoice data access capabilities. Service Consumers A, B, and C then need to be
redesigned to only access the chosen invoice-related service. Because Service Consumer
D does not rely on an invoice-related service, it is not affected by the Official Endpoint
pattern and can continue to access the accounting database directly. The Service
Abstraction principle can be further applied to hide the existence of the shared accounting
database and other implementation details from current and future service consumers.
B. One of the invoice-related services needs to be chosen as the official service providing
invoice data access capabilities. Service Consumers A, B, and C then need to be
redesigned to only access the chosen invoice-related service. Service Consumer D also
needs to be redesigned to not access the shared accounting database directly, but to also
perform its data access by interacting with the official invoice-related service. The Service
Abstraction principle can be further applied to hide the existence of the shared accounting
database and other implementation details from current and future service consumers.
C. None of the above.
D. Because Service Consumers A, B, and C are already carrying out their data access via
published contracts, they are not affected by the Official Endpoint pattern. Service
Consumer D needs to be redesigned to not access the shared accounting database
directly, but to perform its data access by interacting with the official invoice-related service.
The Service Abstraction principle can be further applied to hide the existence of the shared
accounting database and other implementation details from current and future service
consumers.
正解:B



 PDF版 Demo
PDF版 Demo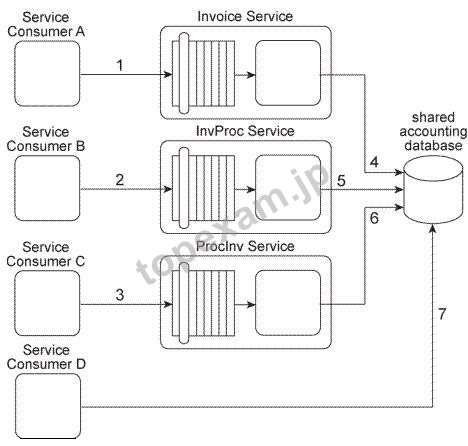






 品質保証TopExamは我々の専門家たちの努力によって、過去の試験のデータが分析されて、数年以来の研究を通して開発されて、多年の研究への整理で、的中率が高くて99%の通過率を保証することができます。
品質保証TopExamは我々の専門家たちの努力によって、過去の試験のデータが分析されて、数年以来の研究を通して開発されて、多年の研究への整理で、的中率が高くて99%の通過率を保証することができます。 一年間の無料アップデートTopExamは弊社の商品をご購入になったお客様に一年間の無料更新サービスを提供することができ、行き届いたアフターサービスを提供します。弊社は毎日更新の情況を検査していて、もし商品が更新されたら、お客様に最新版をお送りいたします。お客様はその一年でずっと最新版を持っているのを保証します。
一年間の無料アップデートTopExamは弊社の商品をご購入になったお客様に一年間の無料更新サービスを提供することができ、行き届いたアフターサービスを提供します。弊社は毎日更新の情況を検査していて、もし商品が更新されたら、お客様に最新版をお送りいたします。お客様はその一年でずっと最新版を持っているのを保証します。 全額返金弊社の商品に自信を持っているから、失敗したら全額で返金することを保証します。弊社の商品でお客様は試験に合格できると信じていますとはいえ、不幸で試験に失敗する場合には、弊社はお客様の支払ったお金を全額で返金するのを承諾します。(
全額返金弊社の商品に自信を持っているから、失敗したら全額で返金することを保証します。弊社の商品でお客様は試験に合格できると信じていますとはいえ、不幸で試験に失敗する場合には、弊社はお客様の支払ったお金を全額で返金するのを承諾します。( ご購入の前の試用TopExamは無料なサンプルを提供します。弊社の商品に疑問を持っているなら、無料サンプルを体験することができます。このサンプルの利用を通して、お客様は弊社の商品に自信を持って、安心で試験を準備することができます。
ご購入の前の試用TopExamは無料なサンプルを提供します。弊社の商品に疑問を持っているなら、無料サンプルを体験することができます。このサンプルの利用を通して、お客様は弊社の商品に自信を持って、安心で試験を準備することができます。
