質問 1:When an application is retrieving a credential from Conjur, the application authenticates to Follower A.
Follower B receives the next request to retrieve the credential.
What happens next?
A. The Coniur Token is stateful and Follower B redirects the request to Follower A to satisfy the request.
B. The Coniur Token is stateless and Follower B is able to validate the Token and satisfy the request.
C. The Coniur Token is stateful and Follower B is unable to validate the Token promptinq the application to re-authenticate.
D. The Coryur Token is stateless and Follower B redirects the request to Follower A to satisfy the request.
正解:B
解説: (Topexam メンバーにのみ表示されます)
質問 2:Refer to the exhibit.

How can you confirm that the Follower has a current copy of the database?
A. Retrieve the credential from a test application on the Leader cluster; then retrieve against the Follower and compare if they are accurate.
B. Compare the pgcurrentxlog_locationlocation from the Leader to the Follower you need to validate against.
C. Count the number of components in pgstartreplication and compare this to the total number of Followers in the deployment.
D. Validate that the Follower container ID matches the node in the info endpoint on the Leader.
正解:B
解説: (Topexam メンバーにのみ表示されます)
質問 3:While retrieving a secret through REST, the secret retrieval fails to find a matching secret. You know the secret onboarding process was completed, the secret is in the expected safe with the expected object name, and the CCP is able to provide secrets to other applications.
What is the most likely cause for this issue?
A. The client certificate fingerprint is not trusted.
B. The service account running the application does not have the correct permissions on the safe.
C. The OS user does not have the correct permissions on the safe
D. The application ID or Application Provider does not have the correct permissions on the safe.
正解:D
解説: (Topexam メンバーにのみ表示されます)
質問 4:While installing the first CP in an environment, errors that occurred when the environment was created are displayed; however, the installation procedure continued and finished successfully.
What should you do?
A. Run setup.exe again and select 'Recreate Vault Environment'. Provide the details of a user with more privileges when prompted by the installer.
B. Continue configuring the application to use the CP. No further action is needed since the successful installation makes the error message benign.
C. Review the lag file 'CreateEnv.loq' and investigate any error messages it contains.
D. Review the PV WA lags to determine which REST API call used during the installation failed.
正解:C
解説: (Topexam メンバーにのみ表示されます)
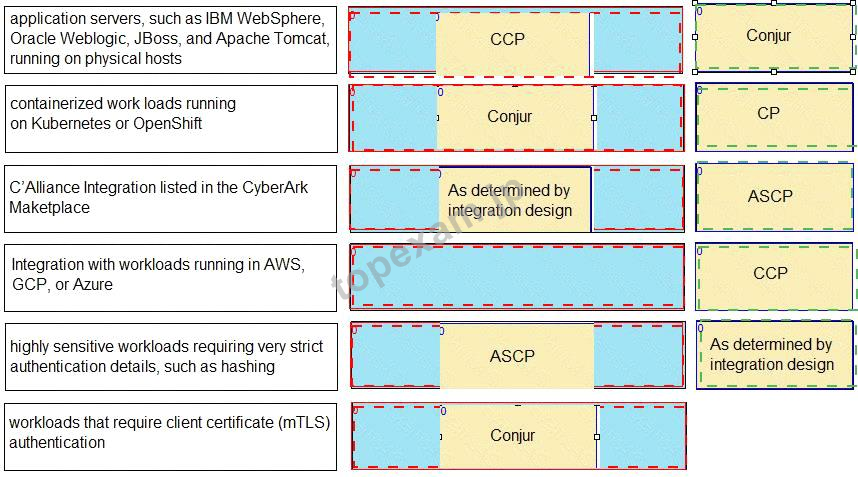
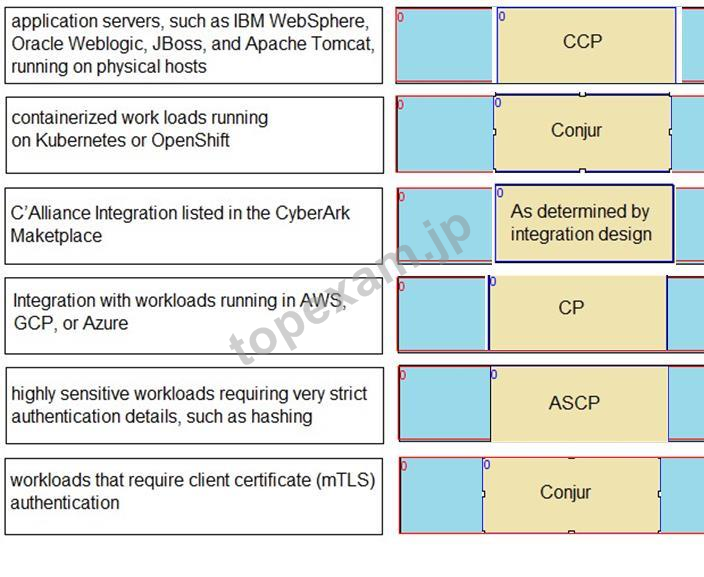
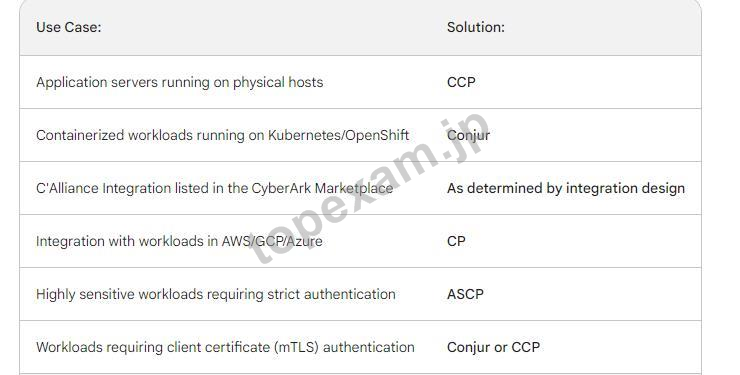
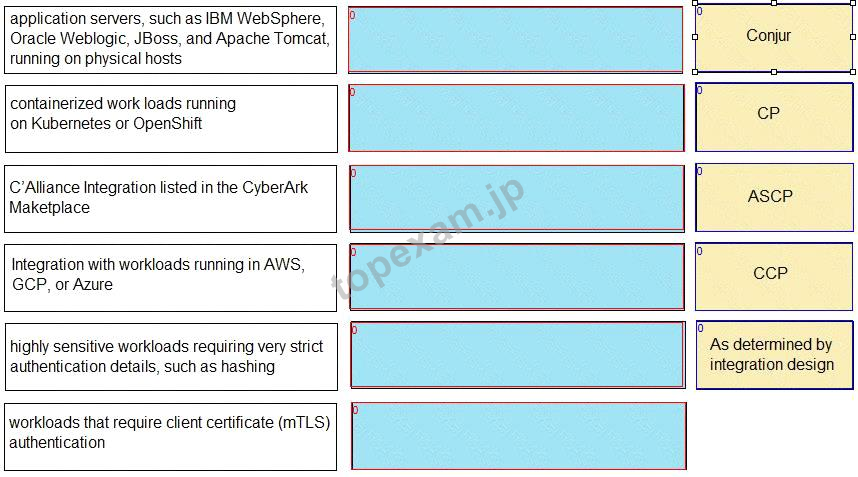
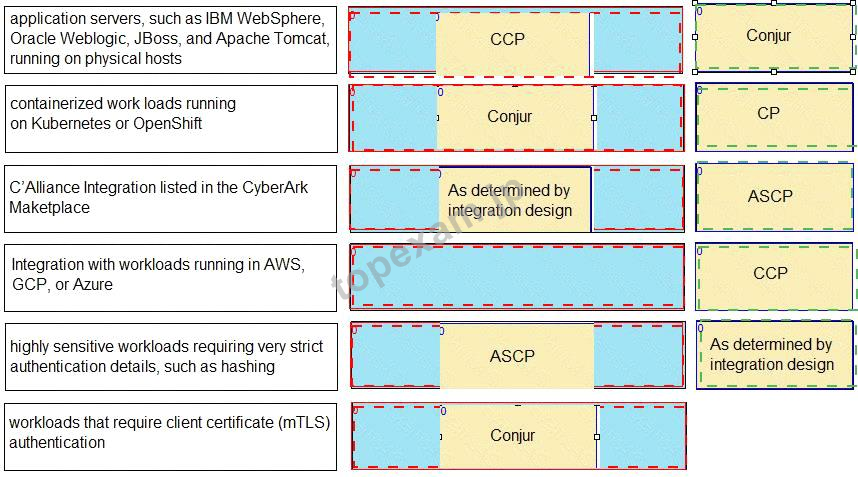
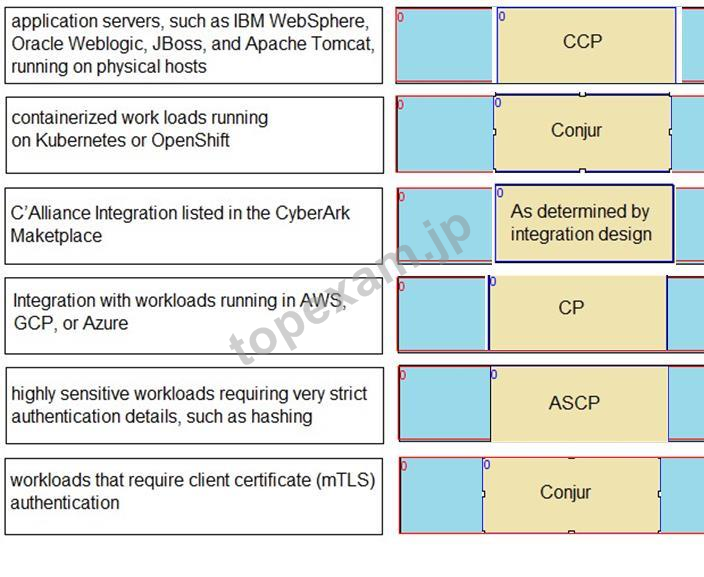
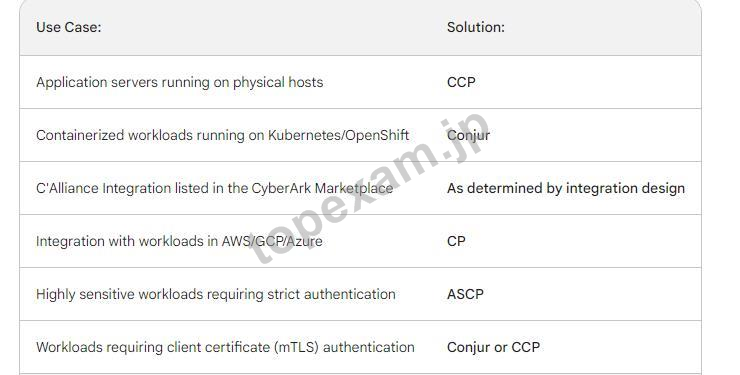
質問 5:Match each use case to the appropriate Secrets Manager Solution.
 正解:
正解:
 質問 6:
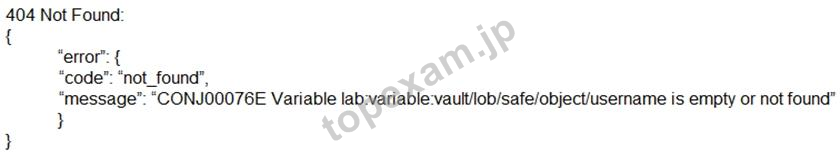
質問 6:When attempting to retrieve a credential managed by the Synchronizer, you receive this error:
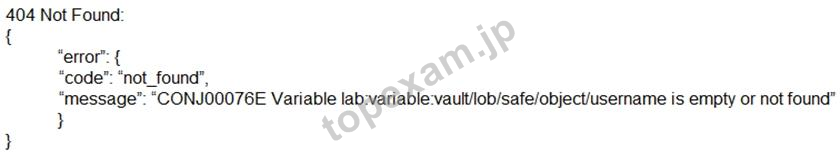
What is the cause of the issue?
A. The Conjur Leader has lost upstream connectivity to the Vault Conjur Synchronizer.
B. The host does not have access to the credential.
C. The Vault Conjur Synchronizer has crashed and needs to be restarted.
D. The path to the credential was not properly encoded.
正解:B
解説: (Topexam メンバーにのみ表示されます)
一年間の無料更新サービスを提供します
君が弊社のCyberArk Secret-Senをご購入になってから、我々の承諾する一年間の更新サービスが無料で得られています。弊社の専門家たちは毎日更新状態を検査していますから、この一年間、更新されたら、弊社は更新されたCyberArk Secret-Senをお客様のメールアドレスにお送りいたします。だから、お客様はいつもタイムリーに更新の通知を受けることができます。我々は購入した一年間でお客様がずっと最新版のCyberArk Secret-Senを持っていることを保証します。
弊社のCyberArk Secret-Senを利用すれば試験に合格できます
弊社のCyberArk Secret-Senは専門家たちが長年の経験を通して最新のシラバスに従って研究し出した勉強資料です。弊社はSecret-Sen問題集の質問と答えが間違いないのを保証いたします。

この問題集は過去のデータから分析して作成されて、カバー率が高くて、受験者としてのあなたを助けて時間とお金を節約して試験に合格する通過率を高めます。我々の問題集は的中率が高くて、100%の合格率を保証します。我々の高質量のCyberArk Secret-Senを利用すれば、君は一回で試験に合格できます。
TopExamは君にSecret-Senの問題集を提供して、あなたの試験への復習にヘルプを提供して、君に難しい専門知識を楽に勉強させます。TopExamは君の試験への合格を期待しています。
弊社は失敗したら全額で返金することを承諾します
我々は弊社のSecret-Sen問題集に自信を持っていますから、試験に失敗したら返金する承諾をします。我々のCyberArk Secret-Senを利用して君は試験に合格できると信じています。もし試験に失敗したら、我々は君の支払ったお金を君に全額で返して、君の試験の失敗する経済損失を減少します。
安全的な支払方式を利用しています
Credit Cardは今まで全世界の一番安全の支払方式です。少数の手続きの費用かかる必要がありますとはいえ、保障があります。お客様の利益を保障するために、弊社のSecret-Sen問題集は全部Credit Cardで支払われることができます。
領収書について:社名入りの領収書が必要な場合、メールで社名に記入していただき送信してください。弊社はPDF版の領収書を提供いたします。
弊社は無料CyberArk Secret-Senサンプルを提供します
お客様は問題集を購入する時、問題集の質量を心配するかもしれませんが、我々はこのことを解決するために、お客様に無料Secret-Senサンプルを提供いたします。そうすると、お客様は購入する前にサンプルをダウンロードしてやってみることができます。君はこのSecret-Sen問題集は自分に適するかどうか判断して購入を決めることができます。
Secret-Sen試験ツール:あなたの訓練に便利をもたらすために、あなたは自分のペースによって複数のパソコンで設置できます。
CyberArk Sentry - Secrets Manager 認定 Secret-Sen 試験問題:
1. You are deploying Kubernetes resources/objects as Conjur identities.
In addition to Namespace and Deployment, from which options can you choose? (Choose two.)
A) Replica sets
B) ServiceAccount
C) Secrets
D) StatefulSet
E) Tokenreviews
2. Match the correct network port to its function in Conjur.

3. When attempting to configure a Follower, you receive the error:

Which port is the problem?
A) 5432
B) 443
C) 1999
D) 1858
4. You modified a Conjur host policy to change its annotations for authentication.
How should you load the policy to make those changes?
A) Use the "update" method (e.g. conjur policy load - -update <branch> <policy-file>).
B) Use the default "append" method (e.g. conjur policy load <branch> <policy-file>).
C) Use the "replace" method (e.g. conjur policy load - -replace <branch> <policy-file>).
D) Use the "delete" method (e.g. conjur policy load - -delete <branch> <policy-file>).
5. How many Windows and Linux servers are required for a minimal Conjur deployment that integrates with an existing CyberArk PAM Vault environment, supports high availability, and is redundant across two geographically disparate regions?
A) 3 Linux servers, 1 Windows server
B) 5 Linux servers, 2 Windows servers
C) 10 Linux servers, 2 Windows server
D) 9 Linux servers, 2 Windows servers
質問と回答:
質問 # 1
正解: B、D | 質問 # 2
正解: メンバーにのみ表示されます | 質問 # 3
正解: A | 質問 # 4
正解: C | 質問 # 5
正解: D |





 PDF版 Demo
PDF版 Demo






 品質保証TopExamは我々の専門家たちの努力によって、過去の試験のデータが分析されて、数年以来の研究を通して開発されて、多年の研究への整理で、的中率が高くて99%の通過率を保証することができます。
品質保証TopExamは我々の専門家たちの努力によって、過去の試験のデータが分析されて、数年以来の研究を通して開発されて、多年の研究への整理で、的中率が高くて99%の通過率を保証することができます。 一年間の無料アップデートTopExamは弊社の商品をご購入になったお客様に一年間の無料更新サービスを提供することができ、行き届いたアフターサービスを提供します。弊社は毎日更新の情況を検査していて、もし商品が更新されたら、お客様に最新版をお送りいたします。お客様はその一年でずっと最新版を持っているのを保証します。
一年間の無料アップデートTopExamは弊社の商品をご購入になったお客様に一年間の無料更新サービスを提供することができ、行き届いたアフターサービスを提供します。弊社は毎日更新の情況を検査していて、もし商品が更新されたら、お客様に最新版をお送りいたします。お客様はその一年でずっと最新版を持っているのを保証します。 全額返金弊社の商品に自信を持っているから、失敗したら全額で返金することを保証します。弊社の商品でお客様は試験に合格できると信じていますとはいえ、不幸で試験に失敗する場合には、弊社はお客様の支払ったお金を全額で返金するのを承諾します。(
全額返金弊社の商品に自信を持っているから、失敗したら全額で返金することを保証します。弊社の商品でお客様は試験に合格できると信じていますとはいえ、不幸で試験に失敗する場合には、弊社はお客様の支払ったお金を全額で返金するのを承諾します。( ご購入の前の試用TopExamは無料なサンプルを提供します。弊社の商品に疑問を持っているなら、無料サンプルを体験することができます。このサンプルの利用を通して、お客様は弊社の商品に自信を持って、安心で試験を準備することができます。
ご購入の前の試用TopExamは無料なサンプルを提供します。弊社の商品に疑問を持っているなら、無料サンプルを体験することができます。このサンプルの利用を通して、お客様は弊社の商品に自信を持って、安心で試験を準備することができます。
